Surety IT provides a monthly security alert of the scams impacting Australian businesses including phishing scams, malware attacks and security breaches/bugs.
Most scams aim to harvest credentials, however there are many common red flags to look out for which include:
- Recipient not being directly addressed
- Sender domains don’t belong to the sites they claim to be from
- Branding not displayed correctly
- Spelling Errors
- Spacing and formatting errors
- Domains aren’t familiar or not legitimate
- Poor English used
- Omit personal details that a legitimate sender would include
- Sent from businesses that you were not expecting to hear from
- Stray PHP tag (“?>”) at the bottom of the email.
You need to be particularly aware of:
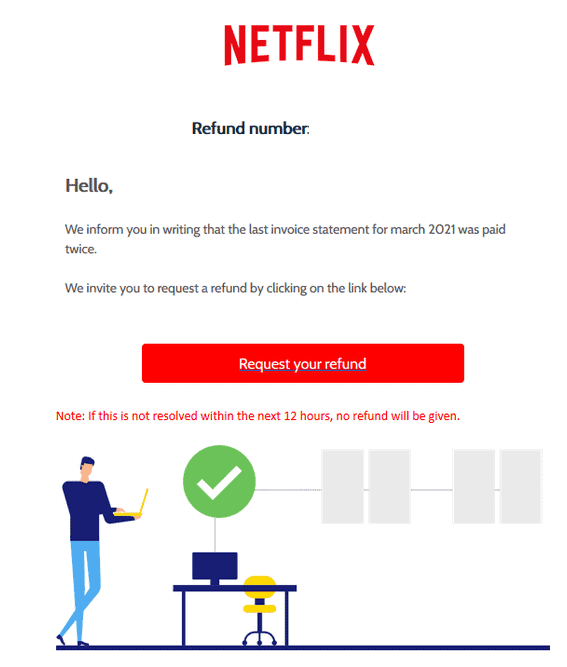
Netflix Spoofed
- Once again Netflix has been spoofed, this email informs users that the ‘last invoice statement for march 2021 was paid twice’
- A link is provided to request a refund within 12 hours.
- Originates from a third-party that is potentially compromised
- Those who click on the link are taken to a compromised site hosted by BigCommerce which redirects to a login page.
- Once users log in, credentials are harvested and taken to another page requesting credit card details and once input are led to a Netflix branded page asking for a one-time code that has been sent to their phone.
- Red flags include: blank subject, inaccurately spelt display name & the recipient isn’t addressed directly.
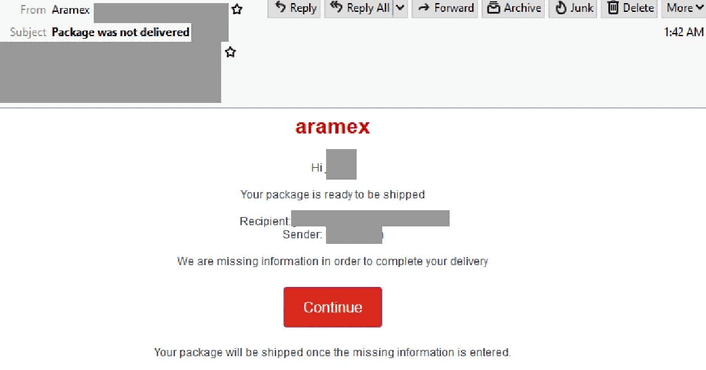
Aramex Impersonated
- Using a display name of ‘Aramex’, this latest phishing scam addresses recipients directly and claims that their package is ready to be shipped.
- Recipients are directed to click on a link to provide some missing information.
- Originates from a server hosted by Digital Ocean and a recently purchased domain from Namecheap.
- Those who click on the link are led to a Google Firebase link which redirects to a secondary page designed to look like Aramex where missing information and ‘pay fee’ is requested.
- Details requested include, email address password, address and multiple different credit card details as the first advises that the card has been declined.
- Red flags include several spacing & formatting errors, domain not belonging to Aramex.
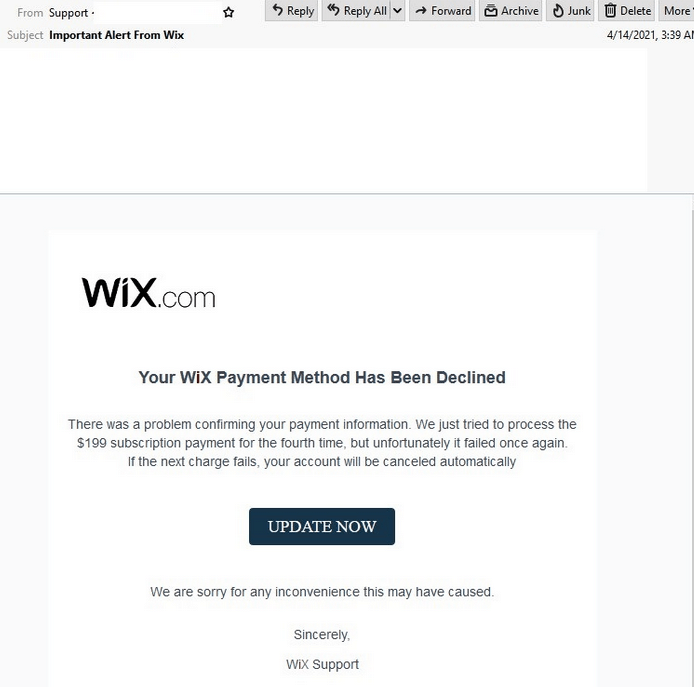
Wix Impersonated
- Malicious email uses a display name of ‘support’ and titled ‘Important Alert From Wix’.
- Recipients are advised that their payment was processed for a fourth time but ‘failed once again’
- A link is provided for recipients to update payment information or risk the account being cancelled.
- Several phishing pages are used should a recipient click the link whereby they are asked to provide login details, credit card details, billing address & email username and password.
- Once inputted, the credentials are harvest for later use and users are redirected to the actual Wix website.
- Red flags include: sender email provided in ‘from’ field doesn’t belong to Wix and domain used to log into the Wix website doesn’t belong to Wix.